ZPanel y Sentora en CentOS 6 x64

ZPanel, un panel de control de alojamiento web popular, se bifurcó en 2014 a un nuevo proyecto llamado Sentora. Aprende a instalar Sentora en tu servidor con este tutorial.
TLS 1.3 is a version of the Transport Layer Security (TLS) protocol that was published in 2018 as a proposed standard in RFC 8446. It offers security and performance improvements over its predecessors.
This guide will demonstrate how to enable TLS 1.3 using the Nginx web server on FreeBSD 12.
A/AAAA/CNAME DNS records for your domain.1.13.0 or greater.1.1.1 or greater.Check the FreeBSD version.
uname -ro
# FreeBSD 12.0-RELEASE
Ensure that your FreeBSD system is up to date.
freebsd-update fetch install
pkg update && pkg upgrade -y
Install necessary packages if they are not present on your system.
pkg install -y sudo vim unzip wget bash socat git
Create a new user account with your preferred username (we will use johndoe).
adduser
# Username: johndoe
# Full name: John Doe
# Uid (Leave empty for default): <Enter>
# Login group [johndoe]: <Enter>
# Login group is johndoe. Invite johndoe into other groups? []: wheel
# Login class [default]: <Enter>
# Shell (sh csh tcsh nologin) [sh]: bash
# Home directory [/home/johndoe]: <Enter>
# Home directory permissions (Leave empty for default): <Enter>
# Use password-based authentication? [yes]: <Enter>
# Use an empty password? (yes/no) [no]: <Enter>
# Use a random password? (yes/no) [no]: <Enter>
# Enter password: your_secure_password
# Enter password again: your_secure_password
# Lock out the account after creation? [no]: <Enter>
# OK? (yes/no): yes
# Add another user? (yes/no): no
# Goodbye!
Run the visudo command and uncomment the %wheel ALL=(ALL) ALL line, to allow members of the wheel group to execute any command.
visudo
# Uncomment by removing hash (#) sign
# %wheel ALL=(ALL) ALL
Now, switch to your newly created user with su.
su - johndoe
NOTE: Replace johndoe with your username.
Set up the timezone.
sudo tzsetup
Install acme.sh.
sudo pkg install -y acme.sh
Check the version.
acme.sh --version
# v2.7.9
Obtain RSA and ECDSA certificates for your domain.
# RSA
sudo acme.sh --issue --standalone -d example.com --ocsp-must-staple --keylength 2048
# ECC/ECDSA
sudo acme.sh --issue --standalone -d example.com --ocsp-must-staple --keylength ec-256
NOTE: Replace example.com in the commands with your domain name.
Create directories to store your certs and keys. We will use /etc/letsencrypt.
sudo mkdir -p /etc/letsencrypt/example.com
sudo mkdir -p /etc/letsencrypt/example.com_ecc
Install and copy certificates to /etc/letsencrypt directory.
# RSA
sudo acme.sh --install-cert -d example.com --cert-file /etc/letsencrypt/example.com/cert.pem --key-file /etc/letsencrypt/example.com/private.key --fullchain-file /etc/letsencrypt/example.com/fullchain.pem
# ECC/ECDSA
sudo acme.sh --install-cert -d example.com --ecc --cert-file /etc/letsencrypt/example.com_ecc/cert.pem --key-file /etc/letsencrypt/example.com_ecc/private.key --fullchain-file /etc/letsencrypt/example.com_ecc/fullchain.pem
After running the above commands, your certificates and keys will be in the following locations:
RSA: /etc/letsencrypt/example.comECC/ECDSA: /etc/letsencrypt/example.com_eccNginx added support for TLS 1.3 in version 1.13.0. FreeBSD 12 system comes with Nginx and OpenSSL that support TLS 1.3 out of the box, so there is no need to build a custom version.
Download and install the latest mainline version of Nginx via the pkg package manager.
sudo pkg install -y nginx-devel
Check the version.
nginx -v
# nginx version: nginx/1.15.8
Check the OpenSSL version against which Nginx was compiled.
nginx -V
# built with OpenSSL 1.1.1a-freebsd 20 Nov 2018
Start and enable Nginx.
sudo sysrc nginx_enable=yes
sudo service nginx start
Now that we have successfully installed Nginx, we are ready to configure it with the proper configuration to start using TLS 1.3 on our server.
Run the sudo vim /usr/local/etc/nginx/example.com.conf command, and populate the file with the following configuration.
server {
listen 443 ssl http2;
listen [::]:443 ssl http2;
server_name example.com;
# RSA
ssl_certificate /etc/letsencrypt/example.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/example.com/private.key;
# ECDSA
ssl_certificate /etc/letsencrypt/example.com_ecc/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/example.com_ecc/private.key;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers 'ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256';
ssl_prefer_server_ciphers on;
}
Save the file and exit with :+W+Q.
Now we need to include example.com.conf in the main nginx.conf file.
Run sudo vim /usr/local/etc/nginx/nginx.conf and add the following line to the http {} block.
include example.com.conf;
Notice the new TLSv1.3 parameter of the ssl_protocols directive. This parameter is only necessary to enable TLS 1.3 on the Nginx server.
Check the configuration.
sudo nginx -t
Reload Nginx.
sudo service nginx reload
To verify TLS 1.3, you can use browser dev tools or SSL Labs service. The screenshots below show Chrome's security tab.
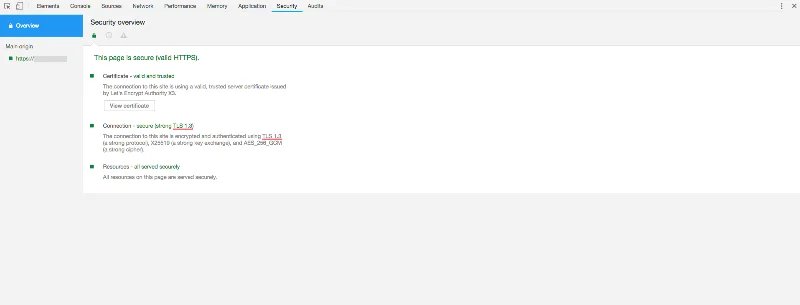
You have successfully enabled TLS 1.3 in Nginx on your FreeBSD server. The final version of TLS 1.3 was defined in August 2018, so there’s no better time to start adopting this new technology.
ZPanel, un panel de control de alojamiento web popular, se bifurcó en 2014 a un nuevo proyecto llamado Sentora. Aprende a instalar Sentora en tu servidor con este tutorial.
Aprende cómo instalar Vtiger CRM, una aplicación de gestión de relaciones con el cliente, en CentOS 7 para aumentar tus ventas y mejorar el servicio al cliente.
Esta guía completa le mostrará cómo configurar un servidor Counter-Strike 1.6 en Linux, optimizando el rendimiento y la seguridad para el mejor juego. Aprende los pasos más recientes aquí.
Los ataques de ransomware van en aumento, pero ¿puede la IA ayudar a lidiar con el último virus informático? ¿Es la IA la respuesta? Lea aquí, sepa que la IA es una bendición o una perdición
ReactOS, un sistema operativo de código abierto y gratuito, está aquí con la última versión. ¿Puede satisfacer las necesidades de los usuarios de Windows de hoy en día y acabar con Microsoft? Averigüemos más sobre este estilo antiguo, pero una experiencia de sistema operativo más nueva.
Whatsapp finalmente lanzó la aplicación de escritorio para usuarios de Mac y Windows. Ahora puede acceder a Whatsapp desde Windows o Mac fácilmente. Disponible para Windows 8+ y Mac OS 10.9+
Lea esto para saber cómo la Inteligencia Artificial se está volviendo popular entre las empresas de pequeña escala y cómo está aumentando las probabilidades de hacerlas crecer y dar ventaja a sus competidores.
Recientemente, Apple lanzó macOS Catalina 10.15.4, una actualización complementaria para solucionar problemas, pero parece que la actualización está causando más problemas que conducen al bloqueo de las máquinas Mac. Lee este artículo para obtener más información
13 Herramientas comerciales de extracción de datos de Big Data
Nuestra computadora almacena todos los datos de una manera organizada conocida como sistema de archivos de diario. Es un método eficiente que permite a la computadora buscar y mostrar archivos tan pronto como presiona buscar.